NS3 is a discrete event packet simulator framework to design a core programming models by C++ language. We offer NS3 in research thesis which mainly for PhD students and research scholars. We develop various research projects with Thesis for PhD scholars. We concentrated on to develop and implement new concepts in network based on user needs. We create thesis and implement projects in networking are simulated and tested by simulation like NS3. We employed more than 90 thesis with various new protocols and algorithm for attack detection, prevention through NS3 simulation. We developed large number of research based application with recent technologies through simulation model.

TIARA Algorithm:
We improve MANET communication by this algorithm called techniques for Intrusion Resistant Ad hoc Routing algorithm (TIARA). This algorithm functioned as group to temper attack impact in network. It works on the following techniques:
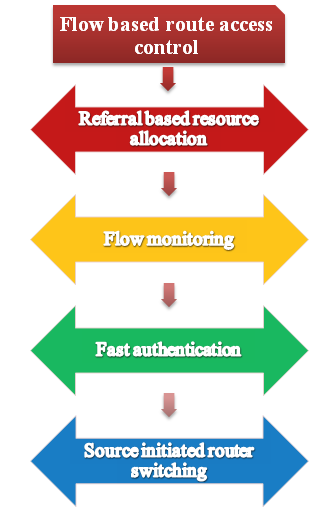
Flow Based Route Access Control (FRAV):
- Flow monitoring.
- Source initiated Router switching.
- Referral based resource allocation.
- Fast authentication.
FRAC Technique:
We implement this technique flow based route access control to control the packets sequence among source and destination node. Every intermediate node retains route policy for entire network to describe an authorized flow of each intermediate node. To detect path failure and informing detected path failure to source node are performed by this technique. For data transmission source node select another route.
Flow Monitoring:
We perform flow monitoring, by encrypt a flow status message as digital signature and sent by routing function as mentioned in Springer Papers. In routing process, we mention source and destination node sequence number using this technique, source node select best route among multiple routes in source and destination.
Fast Authentication:
To authenticate data packets, we implement fast authentication. Every packet in network pointed with path label at specific secret location. This mechanism works on packet label notation. To eradicate traffic analysis attack packet secret location are changed periodically.
Resource Allocation:
We implement this technique to avoid resource depletion attack. It happened when two colluding attacker combined and cooperate through direct link. We provide additional resources from other trusted nodes. To maintain resource we define threshold value for all nodes.
BFTR Algorithm:
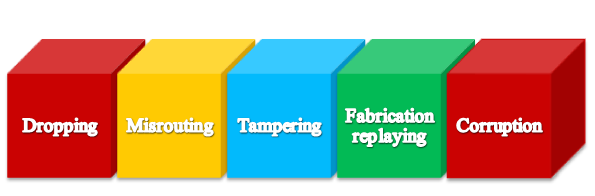
We implement Best Effort Fault Tolerant Routing algorithm which works on authentication principle. By this algorithm, it improve packet delivery ratio using statistics and DSR flooding, we select most shortest and feasible path. By this algorithm, we can ensure end to end packet delivery under attacks such as dropping, misrouting, tampering, fabrication replaying, and corruption resolved by academic projects.